When you think of Internet censorship, you probably think of China or Russia. Maybe you think of India, where Internet shutdowns have accompanied recent farmers' protests.
But the US? Sure, private companies remove content from time to time, but the US government doesn't block access to anything. Right?
In fact, the United States has blocked access to over 1.2 million web domains since 2010. The operation, Operation In Our Sites, is administered by ICE. And domains are seized without due process. How? By exploiting US dominance over core Internet services.
Is it really content blocking?
ICE would probably object to my use of the term “block access to.” It would say that it has “seized” domains, or performed a “takedown.” How is “seizing” a domain different from "blocking" it?
Well, when ICE seizes domains, what they have really done is seize your route to the site. The content's still being served somewhere; the US has just severed your path to it. They do this by taking control of the domain name (e.g., chinaseatbelt.com) and pointing it to an ICE-controlled server [1]. How? Well, the vast majority of websites are run on domains managed by US-based companies called registrars.
In principle, interfering with the route is not meaningfully different from the methods behind Chinese censorship. Almost all censorship methods disrupt users' path to the content rather than removing the content itself [2].
The meaningful difference between US content blocking and everyone else's is this: blocking is local, but seizures are global. When China blocks Google, Google is still accessible outside of China. When, for example, the US helps a publisher “seize” SciHub's domains, SciHub becomes inaccessible worldwide.
Is it really a risk to the Internet?
There are two ways to think about this question. One is what has happened. So far, the US has taken down over 1.2 million websites. We don't have a comprehensive list of the websites taken down [3], but they mostly appear to concern copyright enforcement.
In thinking about risks to the Internet, though, the question is, what could happen? How much of the Internet could the US seize if it wanted to?
Here are some back-of-the-envelope calculations based on the most recent figures from W3Techs:
64.2% of Internet content is served on websites whose registrars are inside US jurisdiction [4]. So, if the US were to flex its jurisdiction, 64.2% of websites could redirect to one of those splash images. That would be a “hard” seizure—it removes your route to the content.
What about companies who have their domain name outside of US jurisdiction—like bit.ly, with their Libyan domain?
Well, sites like bit.ly still need a TLS certificate. If you try to visit a page without one, your browser will display a scary, red lock telling you the page is insecure. If you visit a page whose certificate has been revoked, you'll see an even more frightening error telling you the website might be unsafe.
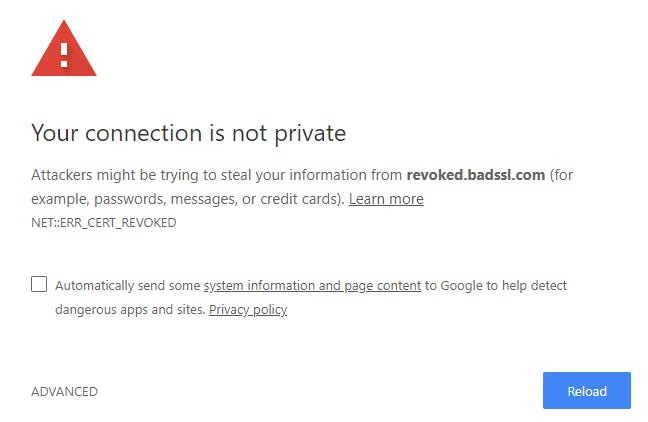
Fortunately for the US, 96.3% of domains—including bit.ly's—rely on US-based certificate authorities. US-based certificate authorities deny certificates to (or revoke existing certificates from) sites when a court order asks them to [5]. That would be a “soft” seizure—it doesn't remove your route to the content, but it makes that route more inconvenient to traverse.
That’s 64% of the Internet susceptible to a hard seizure and 96% to a soft seizure. And that’s before considering the critical infrastructure that’s in US jurisdiction: data centers, DNS servers, chokepoints in BGP paths, physical infrastructure like undersea cables...
Thinking beyond “the splinternet”
When it comes to US control over Internet content, the kinetic energy is low, but the potential energy is extremely high. We don't observe tremendous US control today, but if the US ever changed its policy, its soft power over the Internet is so overwhelming that most websites would likely need to fall in line.
What do we do about it?
The first step is to watch how we talk about threats to the Internet. I've mentioned the phrase “the splinternet” (roughly, the idea is that the Internet is becoming increasingly different in different places). Local website blocking, of the Chinese or Iranian variety, splinters the Internet: it makes different content accessible to different people. On the other hand, seizures do not fragment the Internet: seized content becomes equally inaccessible for everyone. When we talk about the “splinternet,” we imply that the US isn’t part of the problem.
The term “splinternet” risks underplaying the threat of a completely global but completely hegemonic Internet commanded by a single jurisdiction. An Internet that’s global, but globally censored.
Today, the US is the one in charge of the Internet's largest companies. And today, the US isn't seizing large swaths of the Internet. But in both cases, tomorrow is always just around the corner.
In other news…
Last week, I wrote about US dominance over critical Internet infrastructure. I wrote that the US hasn't flexed its power over hosting infrastructures yet, but Konstantinos Komaitis wrote in to correct me:
Actually the US has exercised control over its own infrastructure back in 2010 when Amazon kicked Wikileaks out after being questioned by the Senate for hosting the service.
Soft power. A timely addition to this week's post.
—
Many thanks to Andrew McConachie for kicking me to write about this subject. It got no more than a paragraph in the "limitations" section of my First Monday paper. Thanks also to Chris Hoofnagle and Joeseph Lorenzo Hall for the conversations this week.
Footnotes
[1] http://seizedservers.com/, in case you’re curious.
[2] For examples, see Section II.A in Niaki et al., 2020.
[3] I'm working on collecting a list of domains seized by Operation In Our Sites. If you're interested in contributing or know of existing efforts, please get in touch.
[4] I am continuing to compile an ever-growing dataset of Internet providers by jurisdiction.
[5] Here’s an example of such an order.


